Path uploads your entire iPhone address book to its servers
8 Feb 2012 - Singapore
Update #2
Path has released a new version of the app which asks for permission before it sends your address book to its servers and has blogged about the episode.
Update #1
Dave Morin, the CEO of Path has responded in the comments and I’ve pasted it below. As an aside – never in my wildest dreams did I imagine this to blow up like this. I hope we can keep calm and continue to discuss this sensibly.
Arun, thanks for pointing this out. We actually think this is an important conversation and take this very seriously. We upload the address book to our servers in order to help the user find and connect to their friends and family on Path quickly and effeciently as well as to notify them when friends and family join Path. Nothing more.
We believe that this type of friend finding & matching is important to the industry and that it is important that users clearly understand it, so we proactively rolled out an opt-in for this on our Android client a few weeks ago and are rolling out the opt-in for this in 2.0.6 of our iOS Client, pending App Store approval.
Dave Morin Co-Founder and CEO of Path
Original Post
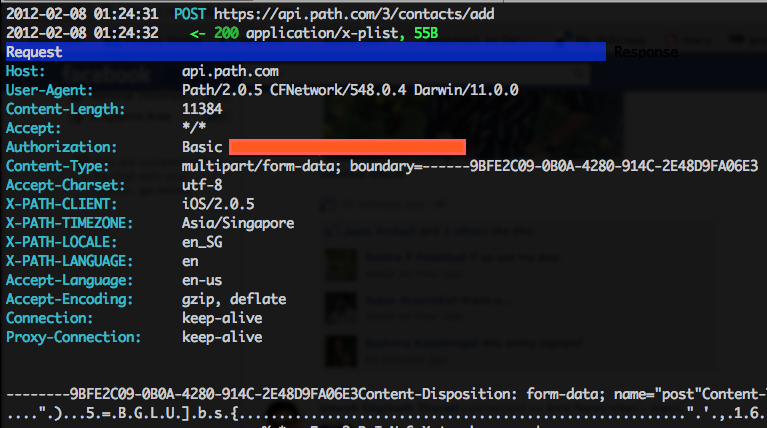
It all started innocently enough. I was thinking of implementing a Path Mac OS X app as part of our regularly scheduled hackathon. Using the awesome mitmproxy tool which was featured on the front page of Hacker News yesterday, I started to observe the various API calls made to Path’s servers from the iPhone app. It all seemed harmless enough until I observed a POST request to https://api.path.com/3/contacts/add.
Upon inspecting closer, I noticed that my entire address book (including full names, emails and phone numbers) was being sent as a plist to Path. Now I don’t remember having given permission to Path to access my address book and send its contents to its servers, so I created a completely new “Path” and repeated the experiment and I got the same result - my address book was in Path’s hands.
Disclaimer
I’m not insinuating that Path is doing something nefarious with my address book but I feel quite violated that my address book is being held remotely on a third-party service. I love Path as an iOS app and I think there are some brilliant people working on it, but this seems a little creepy. I wonder how many other iOS apps actually do the same…
The Trail of Events
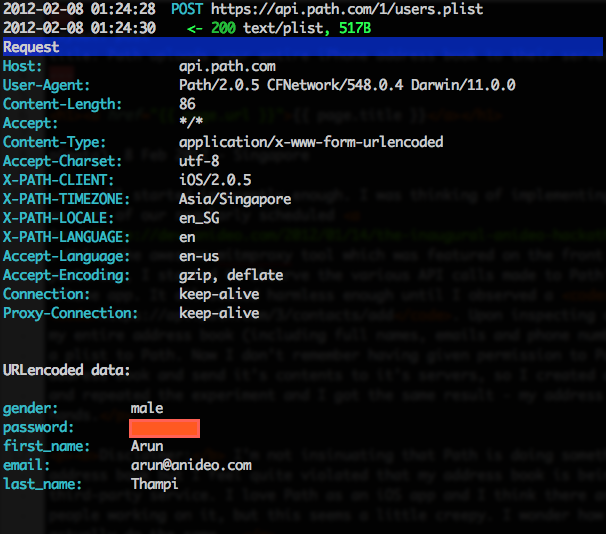
1. https://api.path.com/1/users.plist
As soon as you create a new account to Path, a call is made to https://api.path.com/1/users.plist with your first name, last name, gender and password. An plist is returned which contains the user’s ID as well as other information such as the date of creation.
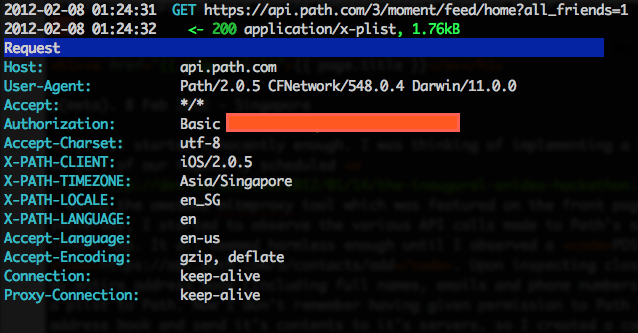
2. https://api.path.com/3/moment/feed/home?all_friends=1
This API call uses basic HTTP authentication (with a certain key) to obtain some metadata about myself - from the binary plist file it looks like it contains my first name, last name, cover photo, profile picture, etc.
3.https://api.path.com/3/contacts/add
This is the actual offending call which uploads my entire address book to Path.
This is followed by normal API calls which among others, updates my location, fetches my activity stream and tracks events within the app using Mixpanel.
How to do this at home
This has been tried out on Mac OS X Lion 10.7.2.
- Download the mitmproxy tool and set it up by going to the folder of mitmproxy and running
sudo python setup.py install. If all goes well, mitmproxy must be available in your $PATH. - Start mitmproxy by running
mitmproxy. - Obtain the IP address of your computer by running
ifconfig en1(or whatever is the interface that you are using). - Set the proxy on your iPhone by going to your wireless settings, setting the proxy to be “Manual”, and set the IP to be your computer’s IP and the port as 8080.